Premium
Fresh spat over Geo Pomona deal

The sources, in separate briefings questioned the “legality” of Harare City Council to continue levying tariffs from residents for a service that it would no longer be providing.
Premium
RBZ mounts crackdown as POS machines flood parallel market

RBZ governor John Mushayavanhu told the Independent that the apex bank cautioned banks to monitor how recipients, who received POS machines, use the electronic gadgets.
By Freeman Makopa
May. 3, 2024
CBZ-ZB merger is a rumour: Vingirai
Business Digest
By Melody Chikono | May. 3, 2024
‘Zim lagging behind on gender policy implementation’
According to the report, the prevalence of gender-based violence is high, and incidences of several forms of GBV remain unchanged.
By Melody Chikono
May. 3, 2024
DWP congress to unlock opportunities for tourism
By Staff Writer
May. 3, 2024
Workers commemorate May Day in despair
By Staff Writer
May. 3, 2024
ZimInd to host capital markets conference
By Melody Chikono
May. 3, 2024
WB mobilising US$20m for women
By Tafadzwa Mhlanga
May. 3, 2024
Rest, good sleep contribute to better health, happiness
By Admin
Feb. 17, 2023
Everyone eligible is encouraged to donate blood, help save lives
By The Independent
Jun. 10, 2022
Cottco seeks US$45m Afreximbank war chest
By Mthandazo Nyoni
May. 3, 2024
Exporters make headway in foreign markets
By Melody Chikono
May. 3, 2024
Hope for lifting ban on OM, PPC chips
By The Independent
Aug. 26, 2022
Without planes, AirZim board won’t perform wonders
By The Independent
Aug. 5, 2022
Power crisis needs urgent attention
By The Independent
Jul. 29, 2022
Don’t print cash for projects
By The Independent
Jul. 22, 2022
Exploring the vibrant world of sports betting in Ethiopia
While the allure of sports betting is undeniable, it's crucial to approach it with caution and responsibility.
By Theindependent
Mar. 11, 2024
Satewave churns out power solutions for Zim
Satewave Technologies director Xiao Feng said the company has several solar solutions to address the current power challenges.
By Staff Writer
Aug. 15, 2023
Liquid Tech to increase tariffs by 50%
By Staff Writer
Mar. 31, 2023
Jotter: Students develop an integrated learning app
By Staff Writer
Mar. 17, 2023
Innovative crowd-investing app ‘PiggyBankAdvisor’ launched
By Staff Writer
Mar. 17, 2023
Meta gives up on NFTs for Facebook and Instagram
By The Verge
Mar. 15, 2023
Reasons To Buy Bitcoin From A Trading Platform
Another fundamental reason behind getting the coins from this particular space is that it provides
By Theindependent
Mar. 2, 2023
Why do banks not want people to rely upon cryptocurrencies?
Cryptocurrency transaction volume is much less than the fiat currencies, leading to a lack of liquidity in the market.
By Theindependent
Feb. 9, 2023
Heritage Golf Academy shines in Botswana

The Heritage Junior Golf Challenge which included golfers from South Africa saw the academy win 15 trophies and 7 medals in a show of hard work, determination and passion.
By Staff Reporter
May. 3, 2024
By Munyaradzi Madzokere
May. 3, 2024
By Sports Reporter
Apr. 26, 2024
New council aims to elevate Zim fashion
By Khumbulani Muleya
May. 3, 2024
Go well Groeblinghoff
By Friedrich Naumann Foundation.
Apr. 26, 2024
Multichoice Talent Factory opening doors
By Yvonne Feresu
Apr. 26, 2024
Bantu Spaceship takes local sounds on a global tour

The band will be going on a European tour in June and July where they are set to perform in France, Germany and Switzerland.
By Khumbulani Muleya
Apr. 26, 2024
International day of jazz: Local concert on the cards
By Khumbulani Muleya
Apr. 19, 2024
Moozy captivates audience at homecoming showcase
By Khumbulani Muleya
Apr. 12, 2024
Herbicides: Bad news for local food security
By The Independent
May. 27, 2022
Dumpsite: Gweru feels the heat
By The Independent
May. 13, 2022
Zim to pay 100% of international hunting revenue to communities
By The Independent
Jun. 10, 2022
.
Videos
Tapera Chikandiwa, Founder Of High Achievers Coach Education Centre In Conversation With Trevor
By The NewsDay
May. 3, 2024
Gugulethu Siso, Founder and CEO of Thumeza Fintech In Conversation With Trevor.
By The NewsDay
May. 3, 2024
Phibion Gwatidzo, Chairman of Baker Tilly Central Africa In Conversation With Trevor
By The NewsDay
May. 3, 2024
Pamela Marwisa In Conversation With Trevor
By The NewsDay
Feb. 28, 2024
Job Sikhala, Zimbabwean Opposition Politician In Conversation With Trevor
By The NewsDay
Feb. 28, 2024
ExtremeWeather: Parts of Harare experienced flash floods on Sunday
By The NewsDay
Dec. 21, 2023
Harare motorists negotiate the city’s treacherous roads
By The NewsDay
Dec. 21, 2023
Dock sheep tail to maintain weight

The most common way of docking tails is by using an elastic and expandable latex ring. The rubber ring is expanded with an elastrator and put over the tail, where it is released.
By Kudakwashe Gwabanayi
Mar. 22, 2024
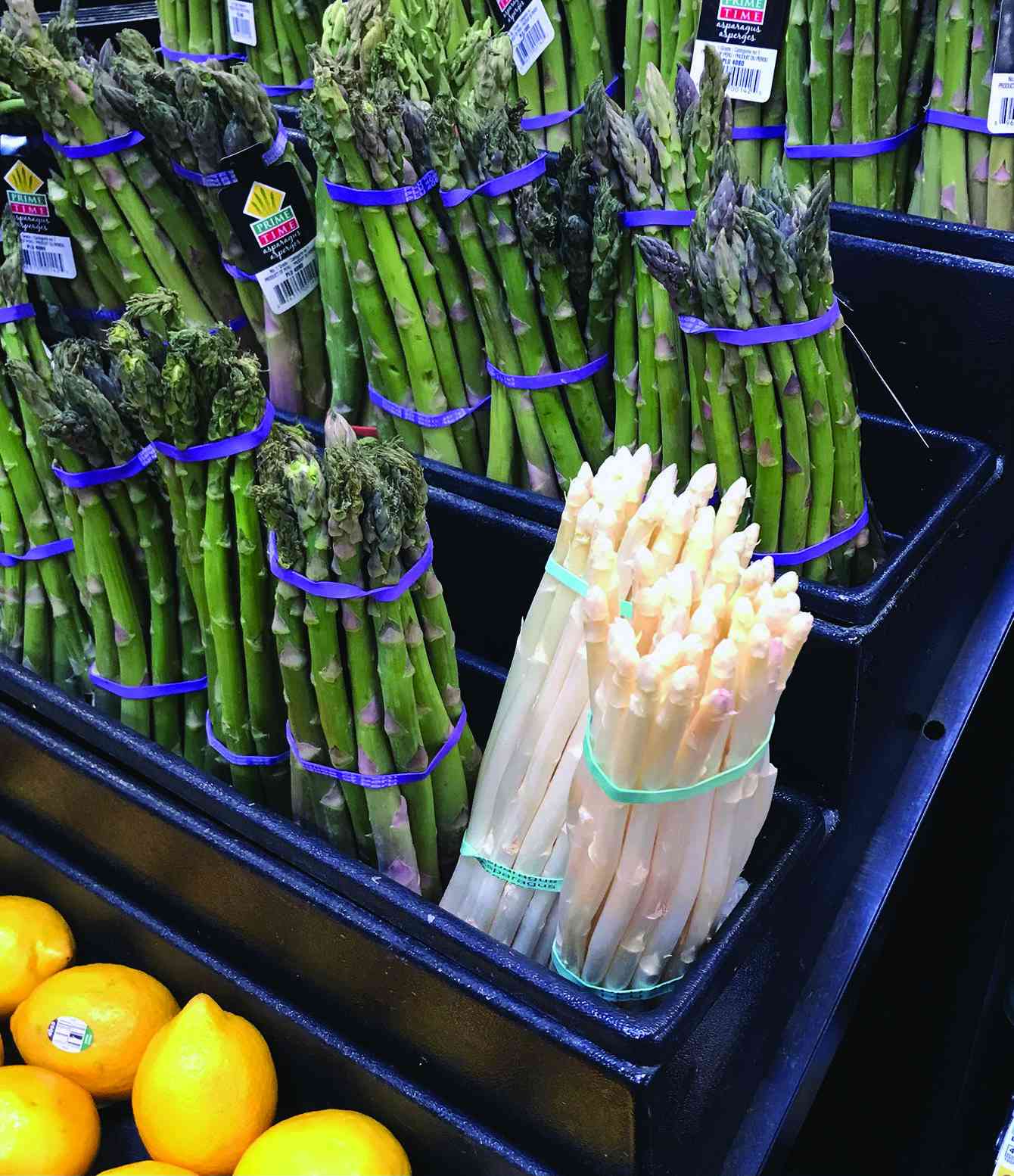
Asparagus worth your while (II)
By Kudakwashe Gwabanayi
Mar. 1, 2024
Why it makes sense to farm meat goats
By Shane Brody
Jul. 7, 2023
How to start a fish farming business
By Kudakwashe Gwabanayi
May. 26, 2023
Climate change is real, be alert
By Kudakwashe Gwabanayi
May. 12, 2023
Sofar hosts concert at Chapungu Sculpture Park
The landscaped garden is a cultural landmark and was established by the late stone sculpture visionary Roy Guthrie.
By Style Reporter
May. 6, 2024
Full house at Mvurwi’s new club official opening
The duo did not disappoint as they gave a scintillating performance in front of the packed Mzansi Lounge.
By Style Reporter
May. 6, 2024
VFEX suspends BNC stocks
By Tatira Zwinoira
May. 5, 2024
Teachers divided over job action.
By Miriam Mangwaya
May. 5, 2024
BCC, TTI streamline parking management
“Clearer visibility of the call centre phone numbers on all tickets issued by TTI for members of the public to contact when clamped or when they have a complaint [sic].”
By Silas Nkala
19h ago
Zacc engages media in gaft fight
Murapa also noted that the National Anti-Corruption Strategy expects the media and the anti-corruption bodies to collaborate so that journalists distribute accurate information.
By Daniel Moyo
19h ago
Byo water crisis set to worsen
By Patricia Sibanda
19h ago
Village heads, chief smoke peace pipe
By Nizbert Moyo
May. 7, 2024
427 Chinese firms set up shop in Zim: Research
By Silas Nkala
May. 7, 2024
Bulawayo road rehab chews US$2m
By Innocent Magondo
May. 7, 2024
Cyanide scandal: Zacc nabs Chinese national

Li Song was nabbed Wednesday afternoon as she came out of the Harare Magistrates Court where she was attending a different matter.
By Staff Reporter
7h ago
By Newsday
19h ago