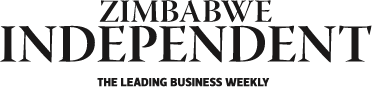
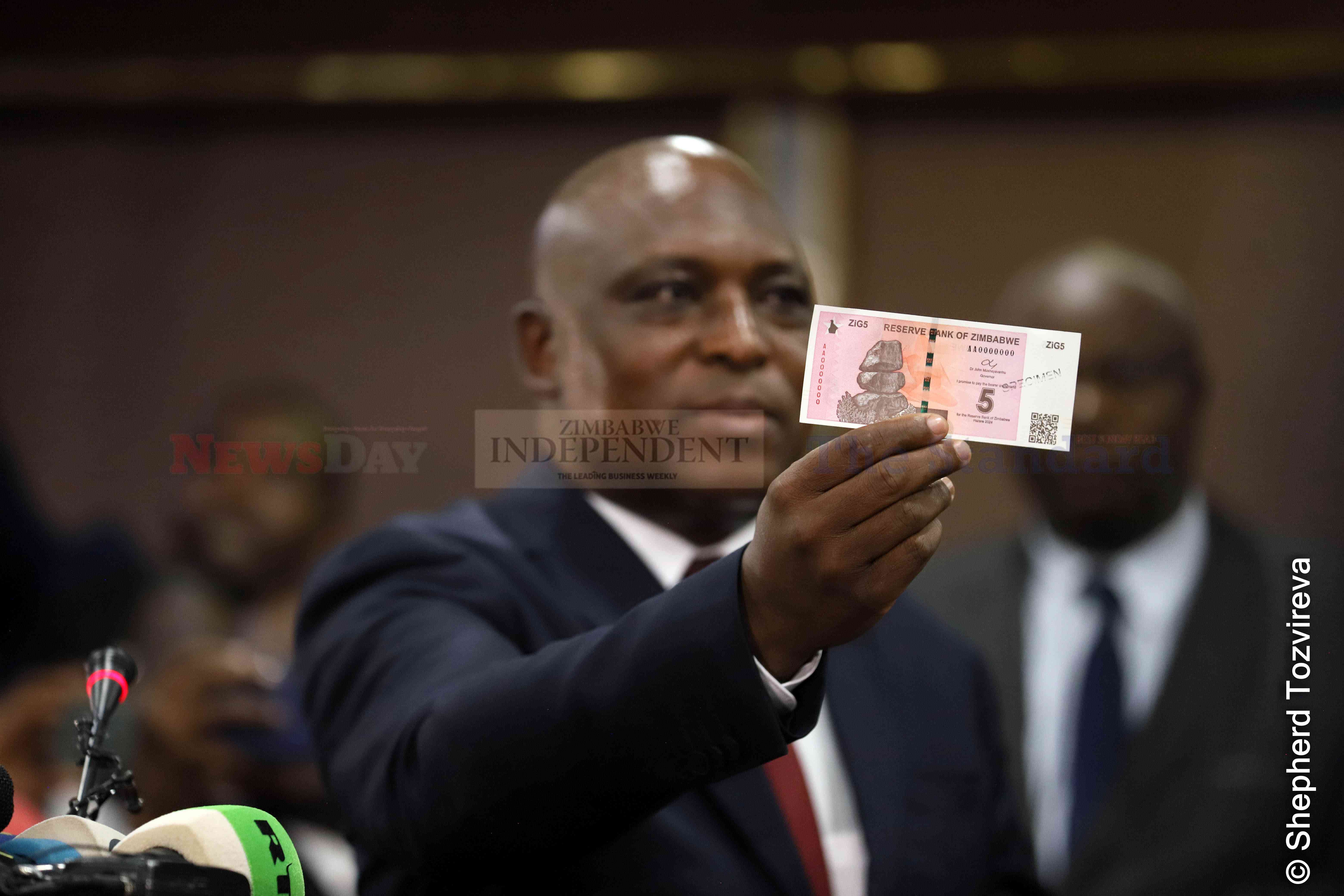
The ZiG was introduced following the rapid depreciation of the Zimbabwe dollar (ZWL).
‘New currency averted systems crash’

It replaced the Zimbabwe dollar (ZWL), which had to be decommissioned after depreciating rapidly against the US dollar, complicating an already dire economic situation.
Advisory sees hefty spinoffs in RTG deal
By Shame Makoshori
Apr. 19, 2024
Telecoms note sharp investment decline
Business Digest
By Melody Chikono | Apr. 19, 2024
‘Inflation forecast unrealistic’
As such, monthly inflation rates are expected to be well below 1%, while annual inflation is projected to close the year below 5%.
By Mthandazo Nyoni
Apr. 19, 2024
Fair game in Zim, China trade
By Julia Ndlela
Apr. 19, 2024
Rest, good sleep contribute to better health, happiness
By Admin
Feb. 17, 2023
Everyone eligible is encouraged to donate blood, help save lives
By The Independent
Jun. 10, 2022
Cottco sets aside US$3,5m for new projects
By Blessed Ndlovu
Apr. 19, 2024
Nissan dealership targets to grow sales by 15%
By Tatira Zwinoira
Apr. 19, 2024
Review of the 2024 Monetary Policy Statement
By Prosper Chitambara
Apr. 12, 2024
Hope for lifting ban on OM, PPC chips
By The Independent
Aug. 26, 2022
Without planes, AirZim board won’t perform wonders
By The Independent
Aug. 5, 2022
Power crisis needs urgent attention
By The Independent
Jul. 29, 2022
Don’t print cash for projects
By The Independent
Jul. 22, 2022
Exploring the vibrant world of sports betting in Ethiopia
While the allure of sports betting is undeniable, it's crucial to approach it with caution and responsibility.
By Theindependent
Mar. 11, 2024
Satewave churns out power solutions for Zim
Satewave Technologies director Xiao Feng said the company has several solar solutions to address the current power challenges.
By Staff Writer
Aug. 15, 2023
Liquid Tech to increase tariffs by 50%
By Staff Writer
Mar. 31, 2023
Jotter: Students develop an integrated learning app
By Staff Writer
Mar. 17, 2023
Innovative crowd-investing app ‘PiggyBankAdvisor’ launched
By Staff Writer
Mar. 17, 2023
Meta gives up on NFTs for Facebook and Instagram
By The Verge
Mar. 15, 2023
Reasons To Buy Bitcoin From A Trading Platform
Another fundamental reason behind getting the coins from this particular space is that it provides
By Theindependent
Mar. 2, 2023
Why do banks not want people to rely upon cryptocurrencies?
Cryptocurrency transaction volume is much less than the fiat currencies, leading to a lack of liquidity in the market.
By Theindependent
Feb. 9, 2023
De Souza banks on speed, agility.

Zimbabwe U20 rugby team head coach, Shaun De Souza is happy with the team’s preparations and looking forward to their tournament opener against Tunisia.
By Austin Karonga
Apr. 19, 2024
By Austin Karonga
Mar. 28, 2024
By Kevin Mapasure
Mar. 28, 2024
By Munyaradzi Madzokere
Mar. 22, 2024
Book Review: African decolonisation in Southern Rhodesian Politics, 1950–1963
By Anotida Chikumbu
Apr. 12, 2024
Moozy captivates audience at homecoming showcase
By Khumbulani Muleya
Apr. 12, 2024
Forbes 30 Under 30 Summit Africa spotlights Zim vegan cuisine

According to forbes.com, featured speakers will include government officials, venture capitalists, CEOs and celebrities.
By Khumbulani Muleya
Apr. 5, 2024
Women take over the stage at Sofar
By Staff Writer
Mar. 28, 2024
Japanese pop culture comes to life in Harare
By Khumbulani Muleya
Mar. 22, 2024
Fawezi wraps up GBV prevention initiative
By Khumbulani Muleya
Mar. 15, 2024
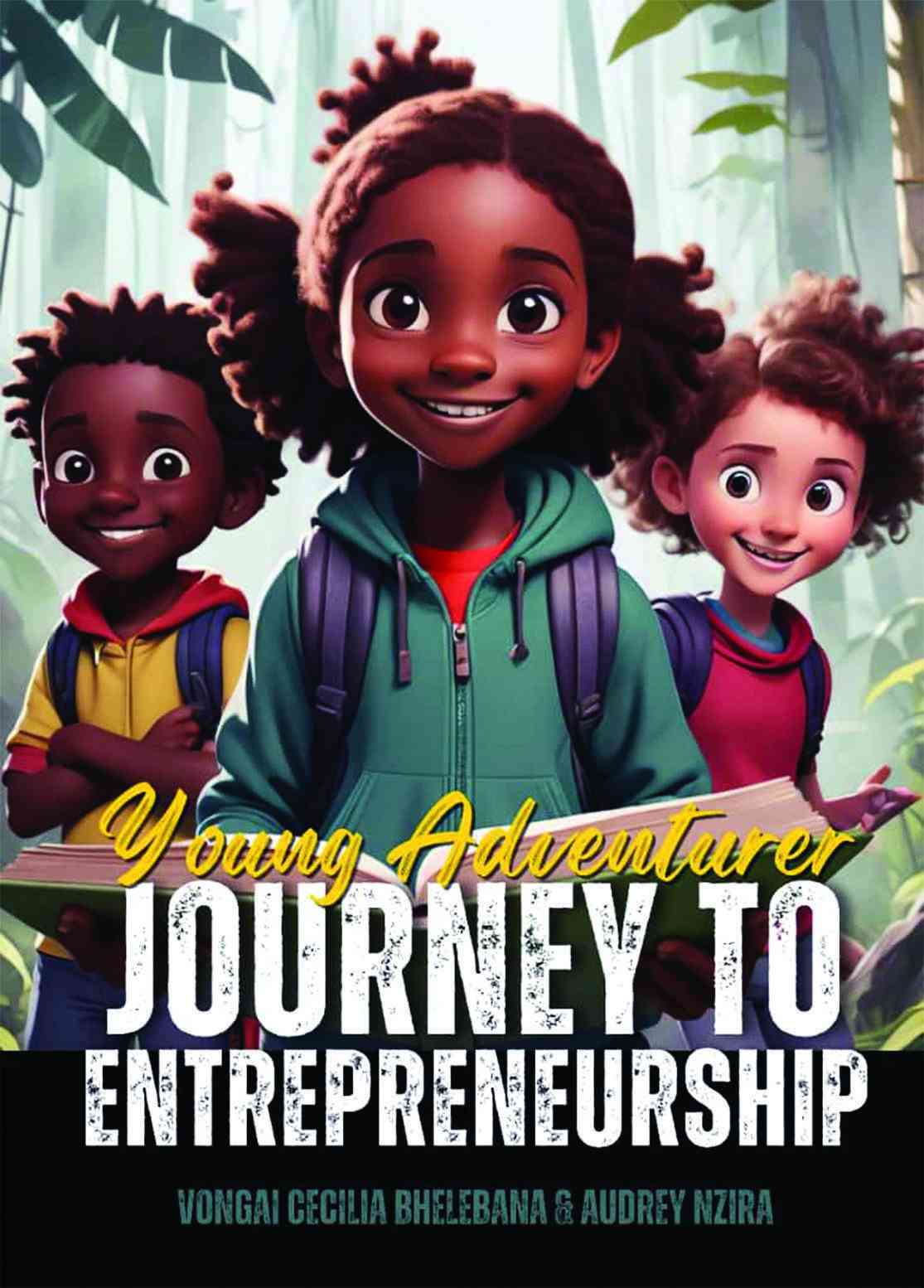
New children’s book a magical adventure
By Khumbulani Muleya
Mar. 15, 2024
Herbicides: Bad news for local food security
By The Independent
May. 27, 2022
Dumpsite: Gweru feels the heat
By The Independent
May. 13, 2022
Zim to pay 100% of international hunting revenue to communities
By The Independent
Jun. 10, 2022
.
Videos
Pamela Marwisa In Conversation With Trevor
By The NewsDay
Feb. 28, 2024
Job Sikhala, Zimbabwean Opposition Politician In Conversation With Trevor
By The NewsDay
Feb. 28, 2024
ExtremeWeather: Parts of Harare experienced flash floods on Sunday
By The NewsDay
Dec. 21, 2023
Harare motorists negotiate the city’s treacherous roads
By The NewsDay
Dec. 21, 2023
Solomon Guramatunhu Day 1
By The NewsDay
Dec. 14, 2023
Sengezo Tshabangu - In Conversation With Trevor
By The NewsDay
Dec. 5, 2023
Welcome to Alpha Media Holdings Zimbabwe - NewsDay - The Standard - The Zim Independent
By The NewsDay
Dec. 5, 2023
Dock sheep tail to maintain weight

The most common way of docking tails is by using an elastic and expandable latex ring. The rubber ring is expanded with an elastrator and put over the tail, where it is released.
By Kudakwashe Gwabanayi
Mar. 22, 2024
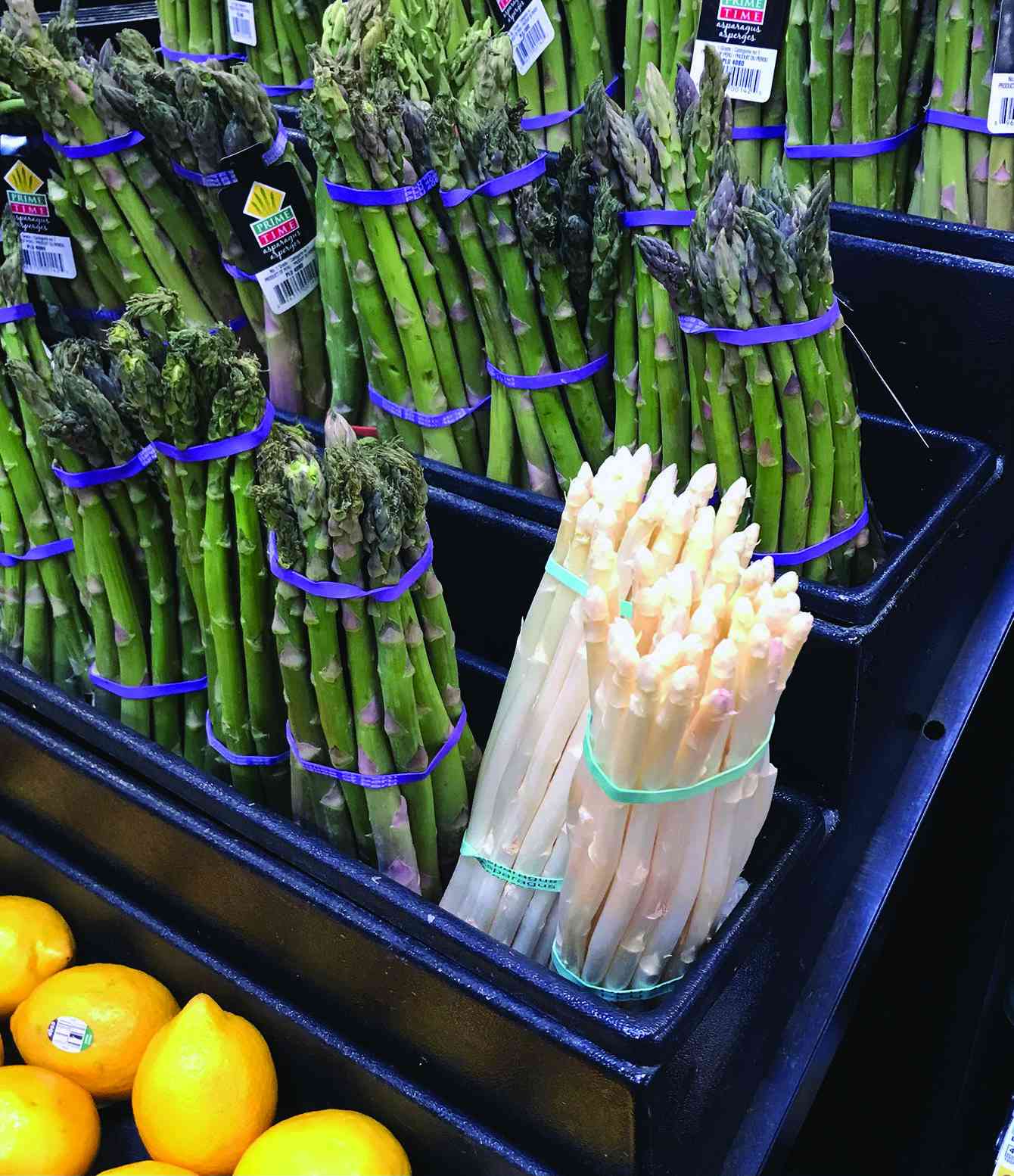
Asparagus worth your while (II)
By Kudakwashe Gwabanayi
Mar. 1, 2024
Why it makes sense to farm meat goats
By Shane Brody
Jul. 7, 2023
How to start a fish farming business
By Kudakwashe Gwabanayi
May. 26, 2023
Climate change is real, be alert
By Kudakwashe Gwabanayi
May. 12, 2023
Baptism of fire for ZiG
Days after the currency was introduced, black market dealers who hold big sums of United States dollar stocks, pegged it at US$1:ZiG18 against the official rate of US$1:ZiG13,56.
By Freeman Makopa
39m ago
Govt invests US$13m in early warning systems
Prosper Matondi, permanent secretary in the ministry of Environment, Climate and Wildlife, said the government had an array of radars that have been installed in about five locations.
By Melody Chikono
Apr. 14, 2024
Out & About: The hum incubating Kehlani’s scales
By Grant Moyo
Apr. 14, 2024
InnBucks pours US$5 million into operations
By Tatira Zwinoira
Apr. 14, 2024
RBZ snubs forex auction bidders
By Melody Chikono
Apr. 14, 2024
GhettoDances: Gossip only breeds confusion and enmity
By Onie Ndoro
Apr. 14, 2024
Lubimbi villagers in limbo over relocation
MIHR director Khumbulani Maphosa yesterday told Southern Eye that the government decided to ignore the appeal adding that the affected families’ future is uncertain.
By Patricia Sibanda
13h ago
12 in court for human trafficking
It is reported that the accused confessed that they were taking the children to South Africa.
By Silas Nkala
13h ago
Zim duo jailed in Botswana
By Silas Nkala
13h ago
Cancer patient sends SOS.
By Jerssie Mpofu
13h ago
Govt urged to walk the talk on Byo water crisis
By Patricia Sibanda
Apr. 19, 2024
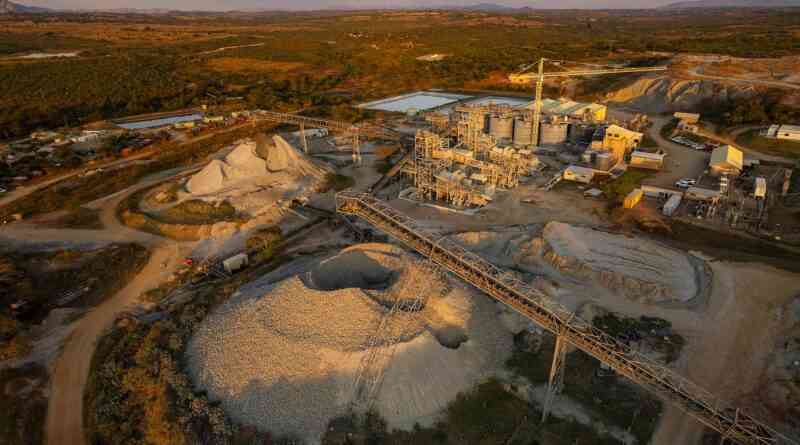
Farmers lose livestock to harmful mining practices
By Rex Mphisa
Apr. 19, 2024
I’ll be the first Zim billionaire under 45: Chivayo

Chivayo has been in the spotlight recently for buying flashy cars for well-known musicians and Johanne Masowe apostolic sect leaders and congregants.
By Freeman Makopa
12h ago